Getting Started
To start using Cyscale, start your Free Trial, or please contact us at [email protected].
Connecting Cloud Accounts/Identity Providers
For specific details on how to integrate with each of the supported providers, follow the links below:
- AWS Integration (cloud)
- Azure Integration (cloud)
- Google Cloud Integration (cloud)
- Alibaba Integration (cloud)
- Okta (IdP)
- Entra ID (IdP)
Sync/Assessment
Once you've connected your cloud environment (or identity provider), Cyscale starts exploring your infrastructure through the provider's APIs. Once Cyscale created a snapshot of your cloud assets, it will perform the assessment. This translates into Cyscale going over the list of controls and looking for assets that fail to meet the requirements.
By default, Cyscale synchronizes your cloud assets and performs the assessment every 24 hours. If you added a connector at 1:24 PM, all subsequent automatic scans will be conducted at 1:24 PM.
Once the assessment is complete, Cyscale will generate the corresponding alerts and store the result in the form of failed assets. These are the basis for determining which controls fail (the ones with failed assets), the security score, and policy/standard status.
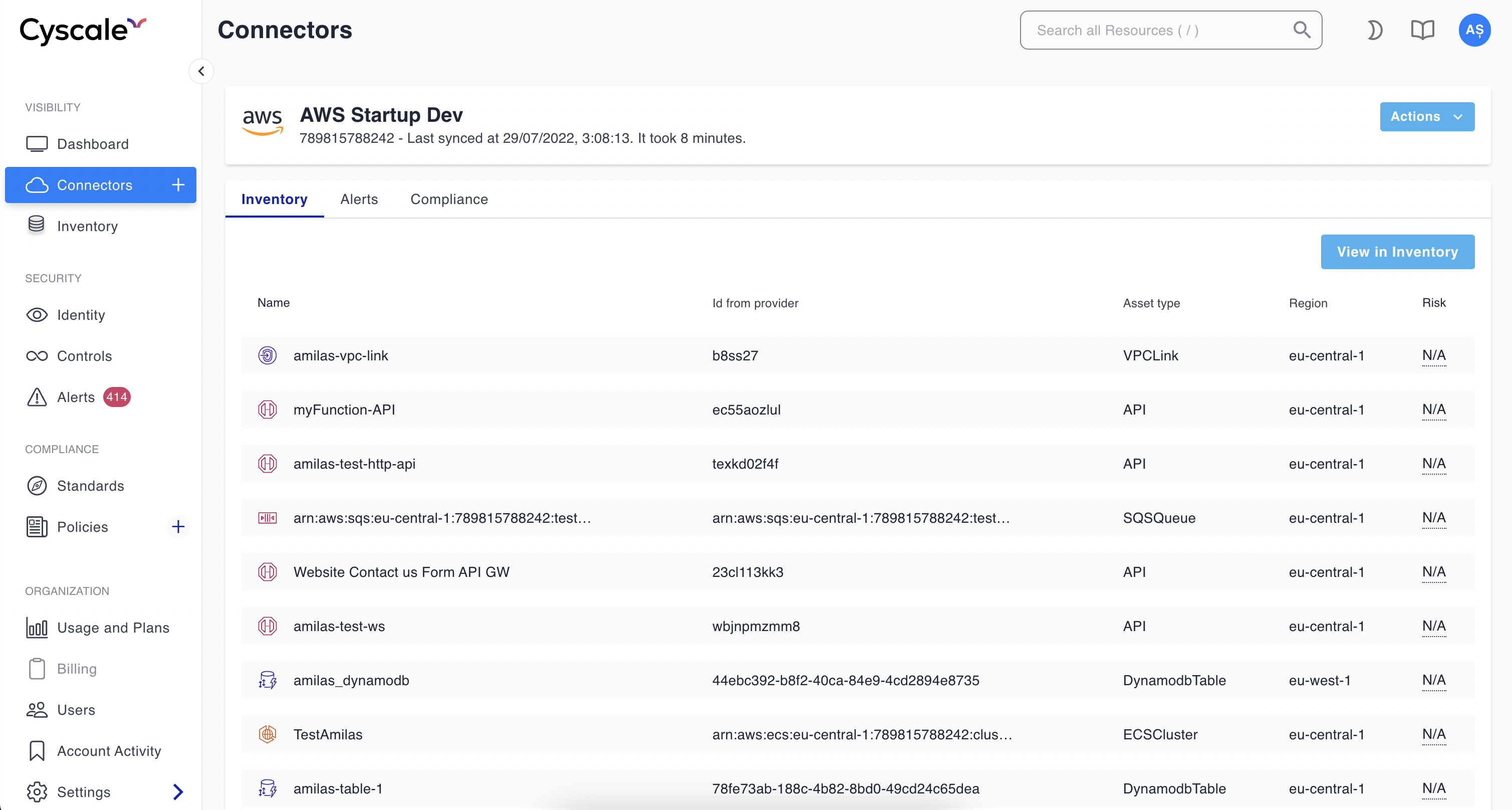
If you go to the Cloud Overview page and the synchronization is still in progress, you should see a loading indicator. Otherwise, you should see some high-level information about the security posture of the connector you just added, similar to the following image:
Besides the scheduled syncs, you can manually trigger the process at any moment by pressing the Sync button. This is helpful if, for example, you changed your infrastructure or want to validate that certain vulnerabilities are indeed fixed. You can find out when Cyscale performed the last sync and how long it took by hovering over the Sync button.
What's Next
At this point you can explore the rest of the platform such as exploring your cloud assets from the visibility section, going through the controls library from the security section, or checking how compliant your infrastructure is with various industry standards such as ISO 27001, SOC 2, PCI DSS, and others.
Additionally, you can always add more connectors.